Whenever you visit a website, a server transmits data to your computer and your computer replies. This data is relatively easy to intercept because it travels through several computers to get to its final destination. By default, this data is sent as ‘plain text’ meaning anyone intercepting it can easily read the information inside. This is a big problem if the data includes sensitive information such as credit card details or personal information.
The solution is for the sender to encrypt the data before it leaves and the recipient to decode the data when it arrives. The encryption is achieved using SSL/TLS technology. As part of the SSL/TLS encryption process, the website’s server sends a key to the visitor’s computer to encrypt information and a certificate. The visitor’s web browser analyses the SSL/TLS certificate to verify that this key belongs to who it says it belongs to.
Certificate Authorities
SSL certificates require a digital signature from a verifying entity. The server owner can use their own signature, creating a so called ‘Self Signed’ certificate but this is near useless for verification purposes. Far more useful is a certificate signed by a specific type of third party called a Certificate Authority (CA). Certificate authorities are companies which issue SSL certificates to entities. They verify the business or organisational entity through processes like emails and phone calls. The value of CA signatures is that they are trusted by most modern web browsers. This allows the connection to proceed seamlessly for the website visitor. Without the implicit approval of the browser, visitors are prompted to manually approve the certificate. This process is jarring and breaks trust.
Usually the server owner obtains the certificate from a CA through purchase, although some CAs provide free certificates. Comodo is the largest Certificate Authority in the world with about a third of all SSL certificates followed by Symantec. Here at Phoenix Web we usually use certificates issued by Trustwave or Let’s Encrpyt as these are integrated into the hosting we provide at VentraIP.
Why use an SSL certificate?
Many payment gateways explicitly require an SSL certificate to be installed on your website. An example is the NAB payment gateway. Even if not needed an SSL cert is a useful addition to your website. Here’s why:
- The SSL certificate provides a psychological reassurance to visitors that your website is secure. Visitors know a website is encrypted and verified because their browser address bar shows a padlock and the
httpprotocol is replaced byhttps.
Google Chrome padlock icon 
Mozilla Firefox padlock icon - Additionally, Google encourages webmasters to use SSL certificates by providing a small boost to the page rank of websites with an SSL certificate. This helps your search engine optimisation, which helps potential visitors find you when searching for keywords related to your business.
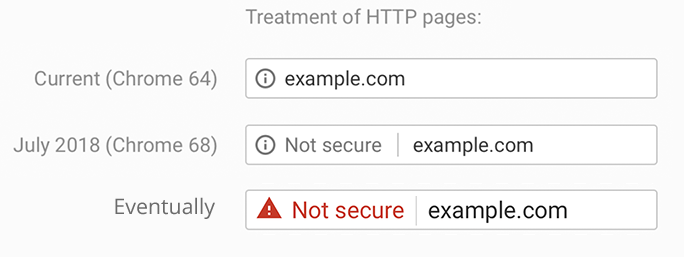
- Most importantly, from July 2018 Google’s Chrome web browser will soon start marking websites without an SSL certificate as insecure. At some point afterwards they will ‘louden’ the Not secure message as per the below image. If visitors see this message while browsing your website it will erode their trust in you. Chrome is by far the most popular web browser with 56% market share so this will be noticed by a large percentage of your visitors. Other browsers will follow Chrome’s lead eventually. The Firefox developers have already said they intend to eventually label HTTP websites insecure. Safari, Edge and the rest will probably follow.
As long as it is installed properly, there is no real downside to installing an SSL certificate on your server. Installing the certificate can be a somewhat complex endeavour. For example, if any external resources are loaded via HTTP, the browser will throw an off-putting error. These resources must be loaded via HTTPS. On the server side, certificates will have to be replaced when they expire. As long as the server is setup correctly, this process is very quick.